-
n8n: An Overview of the Workflow Automation Tool
In business, redundant, day-to-day tasks are known as superfluous tasks. These tasks, which do not require any particular skills, can be detrimental to the productivity of your teams. Many new tools are emerging to automate these tasks and processes and keep employees motivated. Today we are going to present N8N, a free, open source workflow […]
Read more -
NoSQL: All about non-relational databases
NoSQL is a type of database, whose specificity is to be non-relational. These systems allow the storage and analysis of Big Data. Find out everything you need to know: definition, history, functioning, use cases, advantages, training… In the age of Big Data, relational databases are no longer adequate. To handle the immense volumes of data, […]
Read more -
Scapy: Everything you need to know about the Python-based network packaging tool
Scapy is a tool for manipulating computer network packets written in Python. It allows, among other things, the forging or decoding of packets, as well as tasks such as scanning, tracerouting, and unit testing. Discover everything you need to know: advantages, operation, training, and more.
Read more -
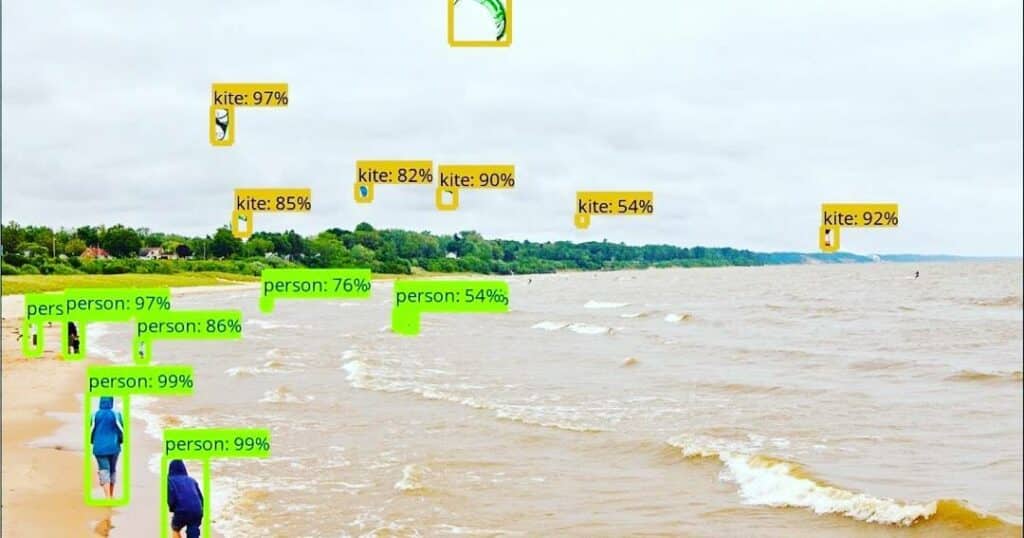
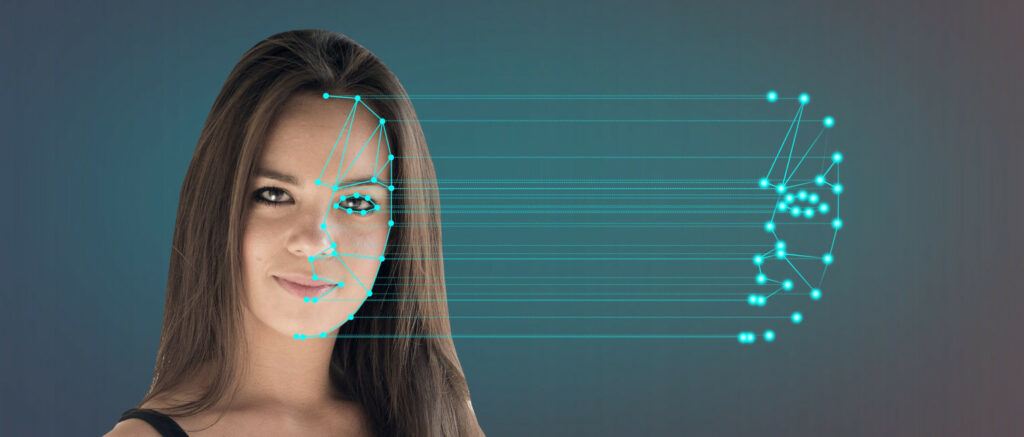
Image Processing: fundamental principles and practical uses
Images contain a wealth of important information. While they are easily discernible to our accustomed eyes, they pose a real challenge in data analysis. The collection of techniques used for this purpose is known as “image processing.” In this article, you will explore the classic algorithms, techniques, and tools for processing data in the form of images.
Read more -
What is Healthcare Data Analytics?
Healthcare Data Analytics is the analysis of health data produced by the medical sector, driving substantial improvements in care and clinical outcomes. Learn everything you need to know about this groundbreaking field: types of data, analysis methods, concrete applications… here’s how Data Science is transforming the modern medical landscape!
Read more -
MAC Address: What is it? What is it used for?
<strong>A MAC (Media Access Control) address is a unique identifier assigned to every network interface of a device. It plays a pivotal role in facilitating communication within <a href="https://liora.io/en/all-about-network-operating-system"><u>local networks</u></a>. MAC addresses are hard-coded into the network hardware during manufacture, serving a vital function in the identification of devices within a network.</strong>
Read more -
Prompt Library: What is an AI prompt library, and how do you create your own?
A Prompt Library is a library of high-quality prompts ready to be used to give instructions to generative AIs such as ChatGPT. It allows you to obtain the best results without having to start writing prompts from scratch for each request. Find out everything you need to know!
Read more -
Zero click attack: How does it work? How can you protect yourself?
A zero-click attack is a cyber attack that allows a computer system to be attacked without the victim even needing to intervene. Find out everything you need to know about this method, which is increasingly used by hackers, how it works and how you can learn to protect yourself!
Read more
The newsletter of the future
Get a glimpse of the future straight to your inbox. Subscribe to discover tomorrow’s tech trends, exclusive tips, and offers just for our community.